5 Common Vendor Management Myths
Author: Michael Cohn
In my many visits and interactions with clients, prospects, competitors, and industry pundits, I hear things that get me thinking. Recently, some of these conversations have focused on common myths related to vendor management.
Regarding vendor management, the regulations are unambiguous in what is expected – at a high level. The devil is in the details, though. And at times, these very details overwhelm us and sometimes trip us over.
Here are 5 common myths about vendor management:
1. You can’t start monitoring until you complete your risk assessments
When it comes to vendor monitoring, no regulation states that you have to complete a risk assessment before you can start monitoring. So, risk assessment is an essential step in the vendor management process. You already must know your critical vendors. In addition, you understand what tasks and documents must be monitored regularly, at least for the high-risk vendors. Now, you may start watching these vendors before you complete your risk assessment.
2. You need to monitor all third-party relationships
In vendor relationship management, you don’t have to monitor all third-party relations. As a result, some simple tips on vendor management, in general, might be in order here.
- List all of your vendors in a central place somewhere. This way, you’ll have a complete list of all your third-party relationships.
- Vendor management best practices suggest implementing a strong contract management process for your vendors.
- At a minimum, you should have a contract management process for vendors with an auto-renewal clause.
- This step will help prevent costly contracts from auto-renewing before an internal review.
- At a minimum, you should have a contract management process for vendors with an auto-renewal clause.
- Monitor the high and moderate-risk vendors and use the guidance and risk assessment results to determine which vendors make this prestigious list for your institution.
- The monitoring tasks for each vendor will vary depending on the relevance of the vendor to your operations.
3. You need to monitor all third-party relationships every year
Not all vendors are to be monitored every year. Your risk assessment tool should provide guidance on the frequency of monitoring and the recommended tasks to monitor for the vendors based on the inherent risk ratings. Base your monitoring frequency on this. It will save you a bundle in time, at least.
4. All vendor relationships must be risk assessed and monitored for all tasks
While it is true that I said you need to list all vendors in a central place, you don’t have to risk assess and monitor all of these vendors. The guidance is clear when it asks you to run your vendor relationship through the following lens.
Qualifying Questions:
Based on your responses to these qualifying (or selection) questions and the vendors’ impact on your operations, you identify those vendors that you will be risk assessing and monitoring. Again, depending on the inherent risk of a particular vendor, you will have a different frequency model for ongoing risk assessment and monitoring.
a. New vendor relationship or activities
b. Material financial effect on the organization
c. Performs critical functions
d. Stores accesses, transmits sensitive, customer information
e. Markets financial products or services
f. Performs subprime lending or card payment transactions
g. Increases risk to earnings or capital
5. Cleaners & contractors are GLBA vendors because they have access to the building
Just because a vendor has access to the building does not automatically mean they have access to client and employee confidential information. And therefore, it does not automatically translate to them being Gramm-Leach-Bliley Act (GLBA) classified as requiring detailed monitoring.
What is more relevant with this specific example is what other policies, procedures, and controls you have in your vendor management strategy to prevent a cleaner from having access to confidential information:
- Do you have a clean desk policy? How do you enforce it?
- Do you have periodic employee training on handling confidential data and disposal and destruction of confidential information (paper and electronic)?
And yet, in some instances, for some of you, your cleaner may qualify as a GLBA vendor!
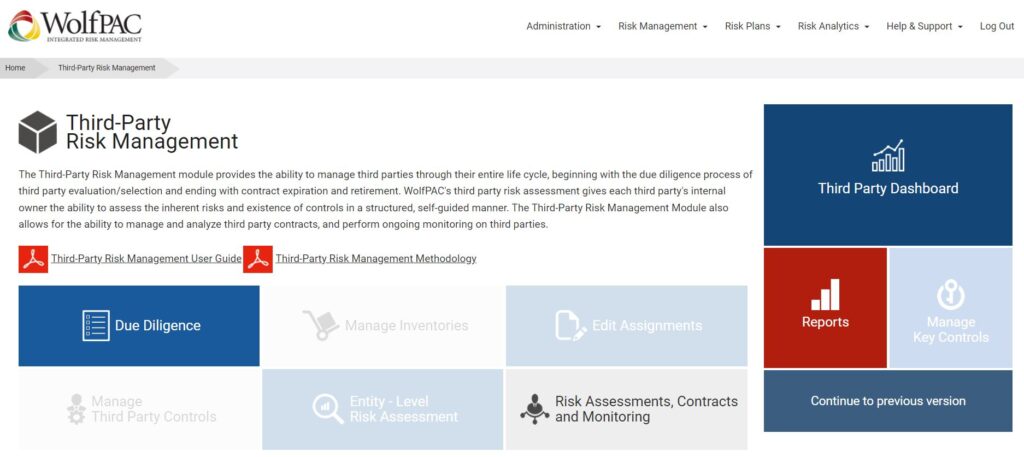
Check Out WolfPAC’s Vendor Management Software Platform
Our platform enables you to develop a comprehensive Third-Party Risk Management program. We arm your organization with the ability to identify high-risk vendors and mitigate those risks.
By automating traditional risk analysis, due diligence, ongoing monitoring, and reporting, our software provides a complete view of your third-party relationship risks from vendors, suppliers, contractors, and other business partners. This new, unprecedented level of visibility, process automation, and data centralization creates significant value for customers by facilitating the following:
- Significant expense reductions,
- Improved vendor performance,
- Successful regulatory exam results, and
- Positive ROI on vendor relationships.
Understanding the value of third-party risk management is only the first step! Next, your organization must bring together the right people, processes, and technologies. Want to learn how we can help your company develop a comprehensive Third-Party Risk Management Program that stands up to the threats of today and tomorrow? Contact us today!
In addition to our legacy offering, we’ve also recently launched WolfPAC Essentials, a new risk management tool that allows lean organizations to build modern risk management programs in three core areas: (1) Vendor Management, (2) IT Risk Management, and (3) Business Continuity Management. Interested parties can start using the offering today for free.
Frequently Asked Questions About Vendor Management
Can you provide examples or case studies illustrating the practical implementation of the strategies suggested for vendor management, particularly in terms of identifying high-risk vendors and mitigating associated risks?
Examples or case studies illustrating the practical implementation of the strategies suggested for vendor management can provide valuable insights into real-world scenarios. By showcasing how organizations have identified high-risk vendors, implemented effective monitoring processes, and mitigated associated risks, readers can gain a better understanding of the challenges and solutions involved in vendor management. These examples could include situations where organizations successfully prevented contract auto-renewals, prioritized monitoring based on risk assessments, and optimized vendor relationships to improve overall operational resilience and regulatory compliance.
How does WolfPAC’s Vendor Management Software Platform address the complexities and challenges associated with vendor management, especially in terms of automating risk analysis, due diligence, and ongoing monitoring?
WolfPAC’s Vendor Management Software Platform addresses the complexities and challenges of vendor management by offering a comprehensive suite of tools and features designed to streamline risk analysis, due diligence, and ongoing monitoring processes. By automating repetitive tasks, centralizing data, and providing actionable insights, the platform enables organizations to proactively identify and address risks associated with their vendor relationships. Moreover, its ability to facilitate regulatory compliance, improve vendor performance, and deliver a positive return on investment makes it a valuable asset for organizations seeking to enhance their vendor management practices in a dynamic business environment.
What are some potential pitfalls or limitations that organizations may encounter when implementing a comprehensive Third-Party Risk Management program, and how can they effectively navigate these challenges to achieve successful regulatory exam results and positive ROI on vendor relationships?
When implementing a comprehensive Third-Party Risk Management program, organizations may encounter potential pitfalls or limitations that require careful consideration and mitigation strategies. These could include challenges related to data accuracy and integrity, resource constraints, regulatory changes, and vendor relationship management. To address these challenges effectively, organizations need to establish clear governance structures, allocate sufficient resources, stay abreast of regulatory developments, and foster open communication and collaboration with vendors. By proactively addressing these potential pitfalls and leveraging technology solutions like WolfPAC’s Vendor Management Software Platform, organizations can enhance their risk management capabilities and achieve successful regulatory exam results and positive ROI on vendor relationships.